
by Alex W. | Nov 16, 2021 | Organisations, Practical, Resilience
Risk Appetite Statements Why are good risk appetite statements so hard to find? or Oils ain’t Oils and nor are Risk Appetite Statements. It’s probably uncontroversial to say that risk appetite statements are better practice for well run organisations. They are...
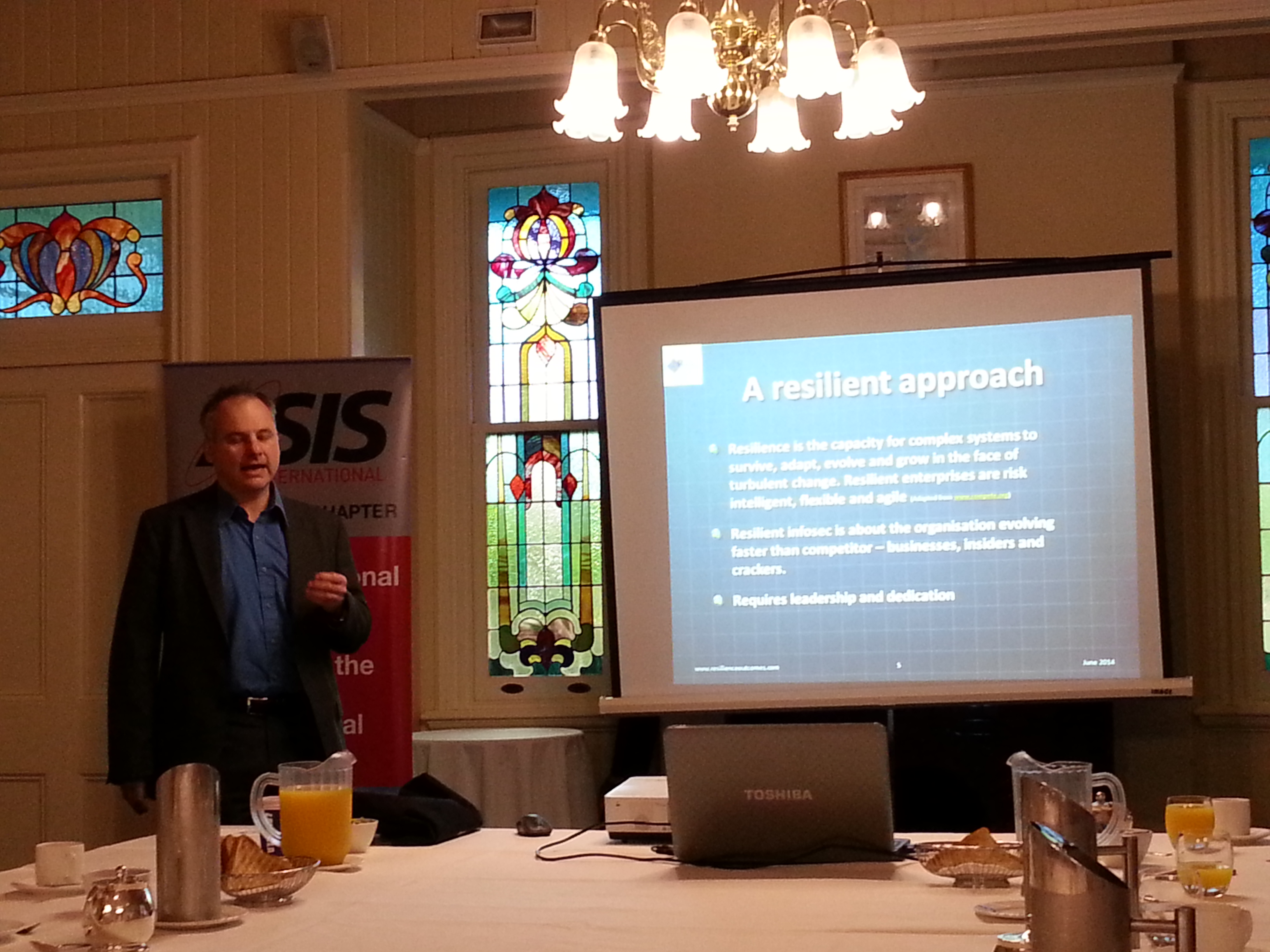
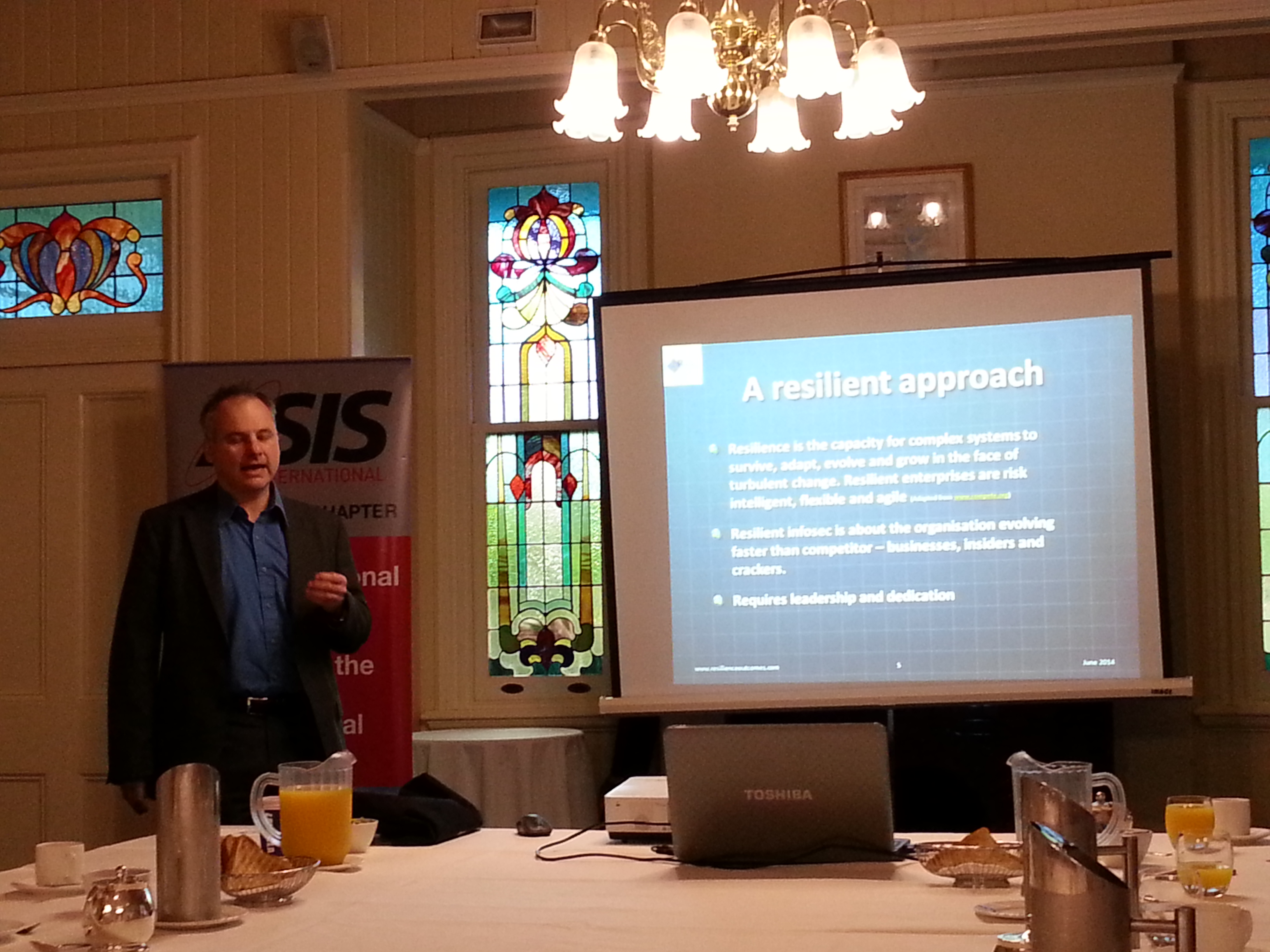
by Alex W. | Jun 12, 2014 | Cybersecurity, Organisations, Resilience
Information Security and Resilience presentation to ASIS QLD Chapter I gave a presentation to the ASIS QLD Chapter yesterday morning. Apart from a couple of minutes spruiking the Australasian Council of Security Professionals, I spent my time talking about the...

by Alex W. | Dec 9, 2013 | Crime, Cybersecurity, Organisations
ENISA has released a good practice guide for CERTs that are tasked with protecting industrial control systems (SCADA). The European Union Agency for Network and Information Security (ENISA) publishes a lot of advice and recommendations on good practice in information...
by Alex W. | Aug 23, 2013 | Organisations, Resilience
A biological approach to organisational resilience By a lapsed microbiologist “Organisational resilience is only achievable through adaptability” Too many leaders start believing their own press and thinking that they are able to predict the future....
by Alex W. | Jul 9, 2013 | Cybersecurity, Organisations
Making strategic decisions about cyber security, or any sort of security needs to be done a the board level. It is difficult to get company boards to focus on strategic issues, despite the fact that this is what they are theoretically meant to do. Companies are busy...




Recently seen here