by Alex W. | Jul 31, 2014 | Organisations, Resilience
ASIS Asia-Pacific Security Forum Alex will be speaking at the ASIS Asia-Pacific Security Forum being held in Singapore 7-9 December 2014. Alex will be talking about: Resilience in an Information Centric World. The best indicators of the future are the events of the...
by Alex W. | Jun 30, 2014 | Community and Society, Cybersecurity, Identity, Privacy
Is it possible to enhance privacy with social login? The likelihood that any Australian Government is going to create an online identity credential now seems distant with the National Trusted Identities Framework (NTIF) almost forgotten. How quickly the Internet...
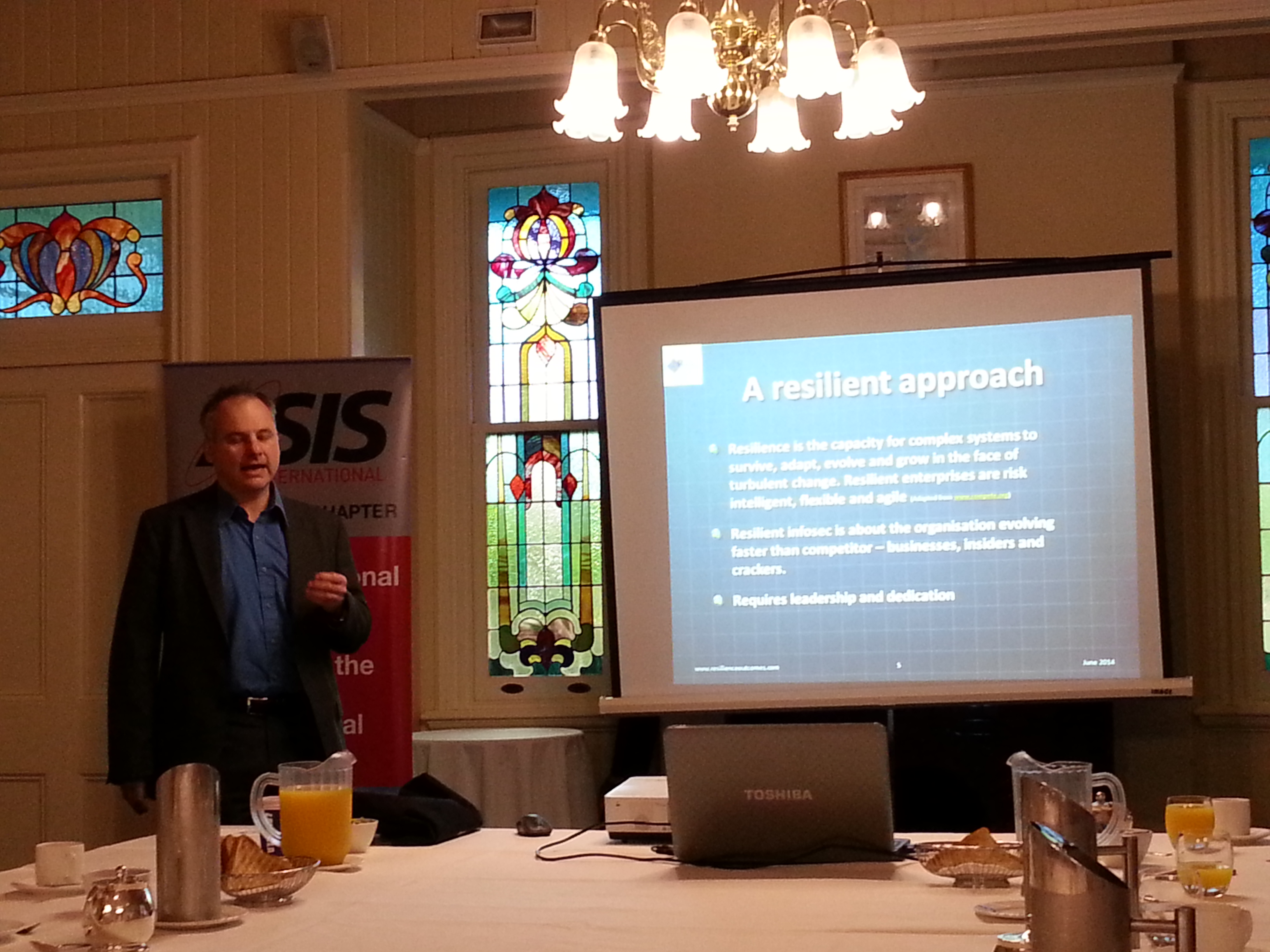
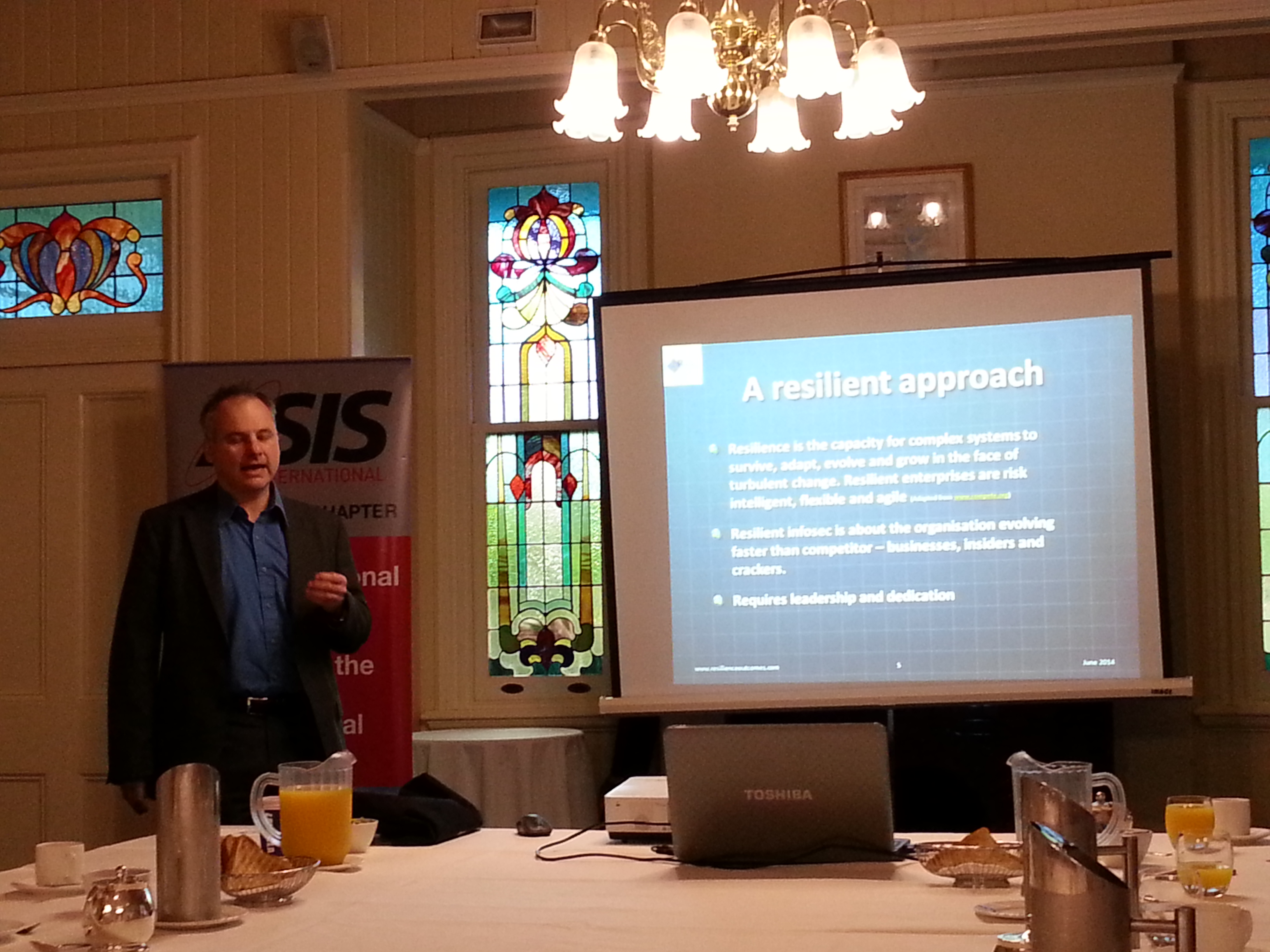
by Alex W. | Jun 12, 2014 | Cybersecurity, Organisations, Resilience
Information Security and Resilience presentation to ASIS QLD Chapter I gave a presentation to the ASIS QLD Chapter yesterday morning. Apart from a couple of minutes spruiking the Australasian Council of Security Professionals, I spent my time talking about the...

by Alex W. | Jun 4, 2014 | Community and Society, Organisations, Resilience
Resilience for organisations is bound to their adaptability to climate change both in the short and long term. A review of US public companies shows a number of climate related risks and costs. Their ability to adapt and become resilient to climate change is starting...
by Alex W. | Mar 12, 2014 | Big data, Fraud, Identity, Organisations, Privacy
Privacy strengthened in Australia The Australian Privacy Principles come into force on 12 March. The APPs extend coverage of privacy laws to most business with turnover of $3 million or more. Fines of $1.7 million are possible for breaches. Australian Privacy...

by Alex W. | Dec 9, 2013 | Crime, Cybersecurity, Organisations
ENISA has released a good practice guide for CERTs that are tasked with protecting industrial control systems (SCADA). The European Union Agency for Network and Information Security (ENISA) publishes a lot of advice and recommendations on good practice in information...

by Alex W. | Nov 7, 2013 | Big data, Community and Society, Cybersecurity, Government large and small, Resilience
Cyber resilience One of the most important aspects of resilience in the information age is understanding the environment in which we exist. Resilience is adaptability in a changing environment, the more we understand that change, the less painful it is. Here are a few...
by Alex W. | Oct 30, 2013 | Cybersecurity, Government large and small
Over-classification in government continues to restrict information sharing according to a report by the US Department of Defense Inspector General. Balance in Information Security I’ve written previously about over-classification and why it needs to be actively...
by Alex W. | Sep 26, 2013 | Big data, Crime, Cybersecurity, Fraud, Identity
Cyber Identity theft service sold personal information on US citizens by compromising multinational consumer and business data aggregators An identity theft service that sells Social Security numbers, birth records, credit and background reports on millions of US...

by Alex W. | Sep 10, 2013 | Community and Society, Government large and small, Identity
The Four Corners program that aired tonight “In Google We Trust” was interesting if a little alarmist as these things sometimes are. But it did make some good points about privacy in the information age. There was an interesting piece of information about...





Recently seen here