by Alex W. | Dec 16, 2014 | Community and Society, Crime, Government large and small, Individual and Personal Resilience, management and leadership
The siege in a chocolate shop in Sydney’s CBD ended early this morning AEST. Three people died, including one purported to be the gunman Haron Monis. There will necessarily be intense scrutiny on the forces used to resolve a violent event. However, it is...
by Alex W. | Jul 19, 2013 | Crime, Fraud, Government large and small, Individual and Personal Resilience, Organisations, Quirky
A culture of entitlement is corrosive in a government agency or any organisation I’ve just come across a USA government document which is both fun to read and educational. Its called the Encyclopedia of ethical failure 2013, its published by the US Defense...
by Alex W. | Sep 11, 2012 | Community and Society, Cybersecurity, Government large and small, Identity, Individual and Personal Resilience
“Trust is the currency of the new economy” You may have heard recently about the efforts being promoted by the USA and Australia amongst others to promote trusted online identities. There are also significant efforts in the private sector to develop online...
by Alex W. | Sep 4, 2012 | Biometrics, Cybersecurity, Identity, Individual and Personal Resilience, Quirky
A legislative approach that defines as ‘sensitive’ any biometric measurement shows a lack of common sense and understanding of the science. A better approach would be to protect those aspects of sensitive personal information (eg sexuality, political...
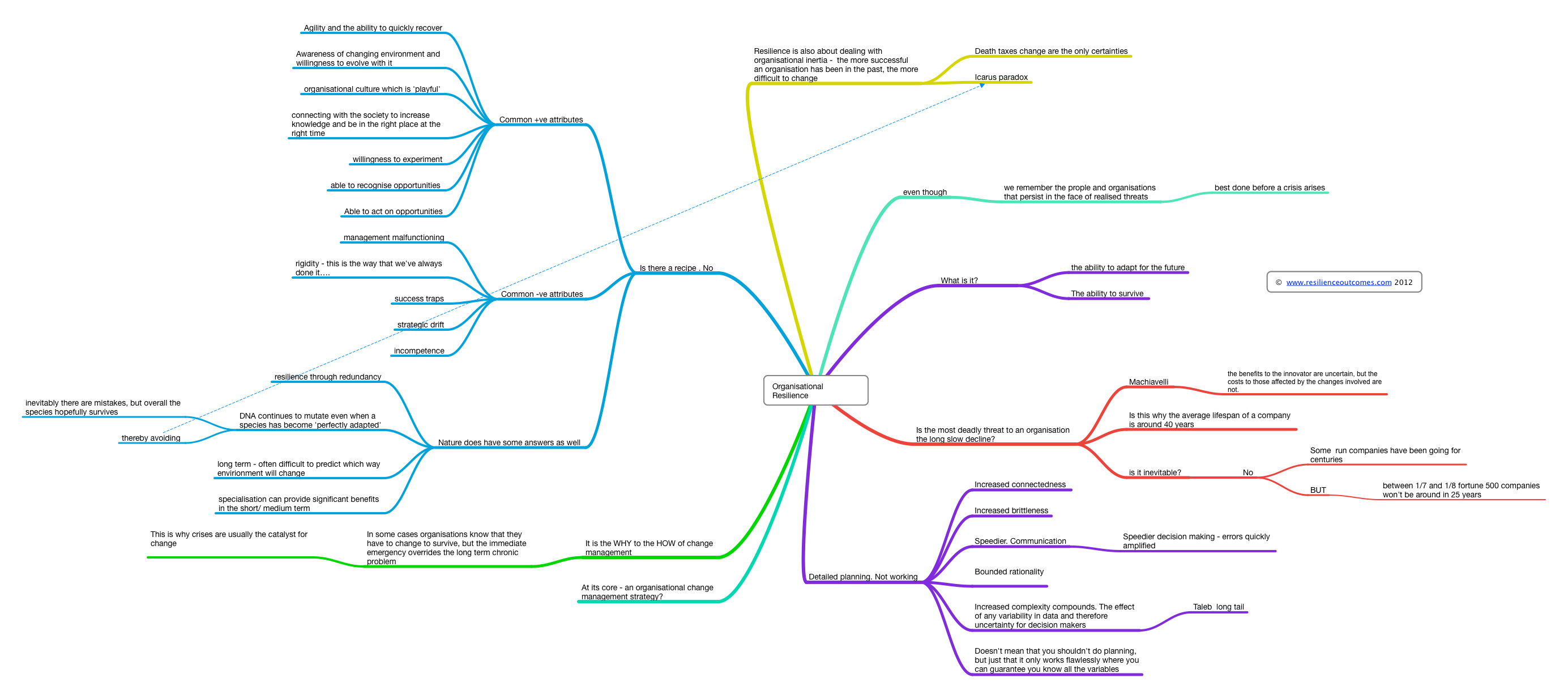
by Alex W. | Aug 16, 2012 | Community and Society, Government large and small, Individual and Personal Resilience, management and leadership, Organisations
Resilience I’ve been trying to summarise organisational resilience into a form that can be visualised for some of the people who I’m working with. The key has been to summarise the thinking on resilience as succinctly as possible. Apart from the diagram...
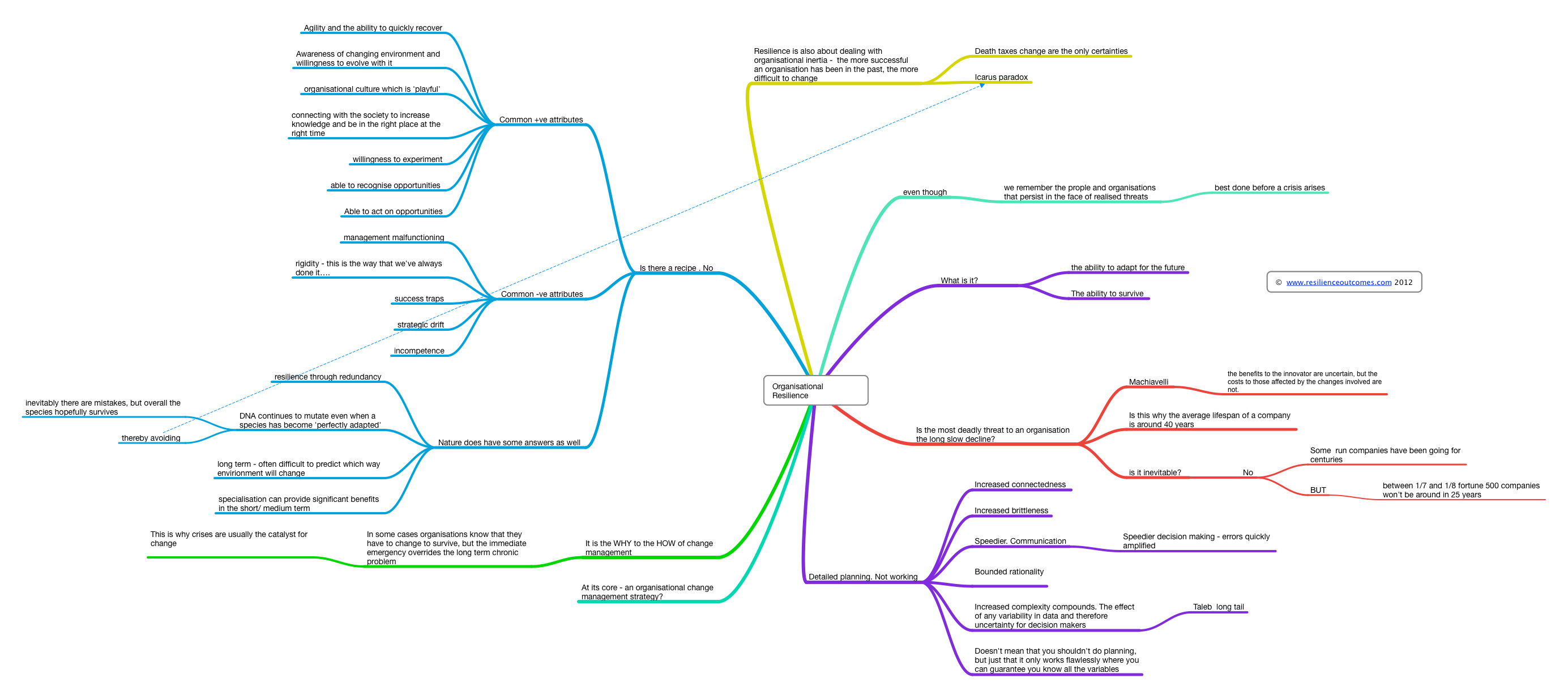

Recently seen here