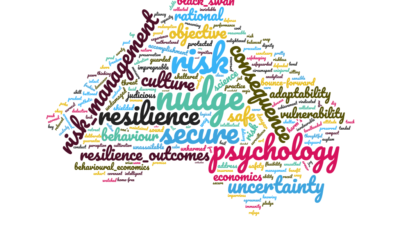
Resilience. EnterpRise and Information security
Things we can do for you
- Audits of company / organisational resilience
- Review of organisational protective security strategy
- Organisational reputation management
- Information privacy and security
- Crisis communications and coordination
- Development of corporate governance strategy
- Independent quality assurance
- Reputation management planning
- Social media strategy
- Crisis Communications
- Corporate protective security and resilience strategy
- Information security strategy for CISOs (Chief Information Security Officer)
- Assessment of agency compliance against the Protective Security Policy Framework (PSPF)
- ISO 27001 Implementation
- Queensland IS18 Implementation and Strategy
- Informations Security Management Systems (ISMS)
- Analysis of projects and organisations against information security best practice
- Computer Incident Response Team development (CSIRT/CERT)
- Cybersecurity strategic posture assessment
- Cloud security strategy
- Identity assurance
- Privacy Impact Assessments
- Biometric interoperability strategy
- GDPR
- Notifiable Data Breaches Scheme
- Information Flow Assessments
- Fraud and Corruption Strategy
- Chemical Biological Radiological (CBRN) strategy
- Personnel Security
- Experienced professional communicators. We
- explain cyber risk to boards
- facilitate holistic risk discussions with executives
- speak to conferences
- lead tutorials
- Executive spearphishing avoidance training
- Design and implementation of phishing campaigns
Resilience Outcomes is a member of the Defence Industry Security Program (DISP)
Our approach
Too often the parts of organisations charged with their protection are seen as a hindrance to the corporate objective – we are not like that. Resilience Outcomes Australia partners with its clients providing smart and effective risk based solutions to strategic security problems. We recognise that security is not an end in itself, but a supporting function to the corporate purpose. We work on evidence, think laterally and are not afraid to swim against the flow.
Our blog
As part of our ongoing commitment to the community, we publish blogposts on security topics of interest to our staff and clients.
People make mistakes
– or why the ‘Pokemon’ approach has to stop
I’ve been watching the unfolding disaster for Optus and more importantly its customers over the last few days.
My initial thoughts are that this seems to be a failure of governance rather than an elaborate ‘Mission Impossible’ style hack.
Security of Critical Infrastructure (SOCI) changes- How does it affect organisations?
Critical Infrastructure ProtectionRecent updates to the Security of Critical Infrastructure (SOCI) Act broaden the definitions of critical infrastructure.The federal Parliamentary Joint Committee on Intelligence and Security (PJCIS) made fourteen recommendations in...
Risk Appetite Statements – most aren’t worth reading
Risk appetite statements are better practice for well run organisations. The kicker is that most organisational risk appetite statements aren’t worth reading.
Achieving Positive Security Outcomes
Thanks to John Bigelow of the ASIAL Insider podcast for the conversation about the ways security managers and executives can use behavioural economics to drive positive security outcomes in their organisations. You can listen to the episode...
Follow
info@resilienceoutcomes.com
Brisbane: 07 3103 1207 (+61 7 3103 1207 outside Australia)
Canberra: 02 6100 2412