Critical Infrastructure Protection
Recent updates to the Security of Critical Infrastructure (SOCI) Act broaden the definitions of critical infrastructure.
The federal Parliamentary Joint Committee on Intelligence and Security (PJCIS) made fourteen recommendations in its report on the Security of Critical Infrastructure (SOCI) Bill 2020 on 29 September 2021. Getting to that point took 9 months, exacerbated in part by the difficulties of operating during a pandemic. The PJCIS recommended that the SOCI Bill be split in two to ensure that elements considered urgent could be legislated.
Two months after the PJCIS report, parliament passed the Security Legislation Amendment (Critical Infrastructure) Act 2021 (Cth) which amends the Security of Critical Infrastructure Act 2018 (Cth). This reflects stage 1 of the reforms. A second, possibly more contentious bill will need to be considered in 2022, most probably after the next election.
Changes passed on 22 November
Expanded definition of Critical Infrastructure
Significantly expanding the definition of critical infrastructure sectors and assets that are defined as critical. This will create positive security obligations for critical infrastructure assets in a broader range of sectors. The Home Affairs Department published draft Critical Infrastructure Asset Definitions in April 2021. These are likely to be finalised in the near future.
https://www.homeaffairs.gov.au/reports-and-pubs/files/critical-infrastructure-asset-definition-rules-paper.pdf More entities providing information to the Register of
More reporting to government
More organisations being defined as critical infrastructure in turn expands the number of reporting entities (entities with effective control) required to provide information for the government to collect in its Register of Critical Infrastructure Assets.
The government has said “The register is designed to improve knowledge so that the Government can proactively assess national security risks related to an asset, and mitigations can be put in place where necessary.“
Mandatory Notification of Cyber Security Incidents
Organisations that are responsible for “critical infrastructure assets” must now report cyber security incidents affecting those assets to the Australian Signals Directorate (ASD), with the aim of facilitating the development of an aggregated threat picture and more completed understanding of cyber security risks to critical infrastructure, and to enable proactive and reactive cyber response options.
Penalties of up to $55,500 (250 penalty units) are possible outcomes for breaches.
Government assistance and intervention measures
The government expressed this aspect as being the most urgent, but it is also those which generated significant concerns by industry during the inquiry. These controversial changes give government a wide power to direct an entity to gather information and take certain actions, or to authorise ASD to intervene in response to cyber-attacks as a “last resort”.
In October 2021, the Australian Information Industry Association and the Information Technology Industry Council wrote to the government with concerns that the legislation is “highly problematic” and would set a “troubling global precedent’.
The government reportedly responded that the changes were similar to fire codes and regulations and likened the ASD’s role to a firebrigade.
This seems to be an oversimplification. Critical infrastructure owners and operators use diverse hardware and software to deliver their services. The idea that ASD, as skilled as it is, could just ride into an organisation in crisis and save the day seems more the stuff of Hollywood than reality. The liability to the government if they stuff it up would seem to be very significant. Other considerations continue to be:
- adequate funding to do this work. ASD will likely be further stretched by this role expansion and Finance won’t be keen to fund it; and
- a structural question, if ASD is to be Australia’s Critical Infrastructure cyber firebrigade, does its stated mission “defend Australia from global threats and help advance Australia’s national interests” still work.
The submissions to the PJCIS are mostly public – https://www.aph.gov.au/Parliamentary_Business/Committees/Joint/Intelligence_and_Security/SOCI/Submissions
The submission from Atlassian is well thought out. They have published a blogpost 8 questions we think should be answered before regulating technology which is worth considering.

What’s next?
The PJCIS recommended Bill Two be postponed due to the current uncertainty as to the application and requirements of the positive security obligations. The precise requirements were due to be prescribed in ‘sector-specific rules’, however these are yet to be developed.
The outstanding aspects are:
- the obligation to adopt and maintain risk management programs – An all-hazards approach;
- the declarations of systems of national significance; and
- the development of enhanced cyber security obligations which are to be defined in delegated legislation. In this regard the PJCIS recognised that the current lack of certainty in relation to these aspects of the regulation creates the spectre of an unknown regulatory burden.
It seems unlikely that these aspects will get much attention until after the next Australian federal election due sometime before end May 2022.


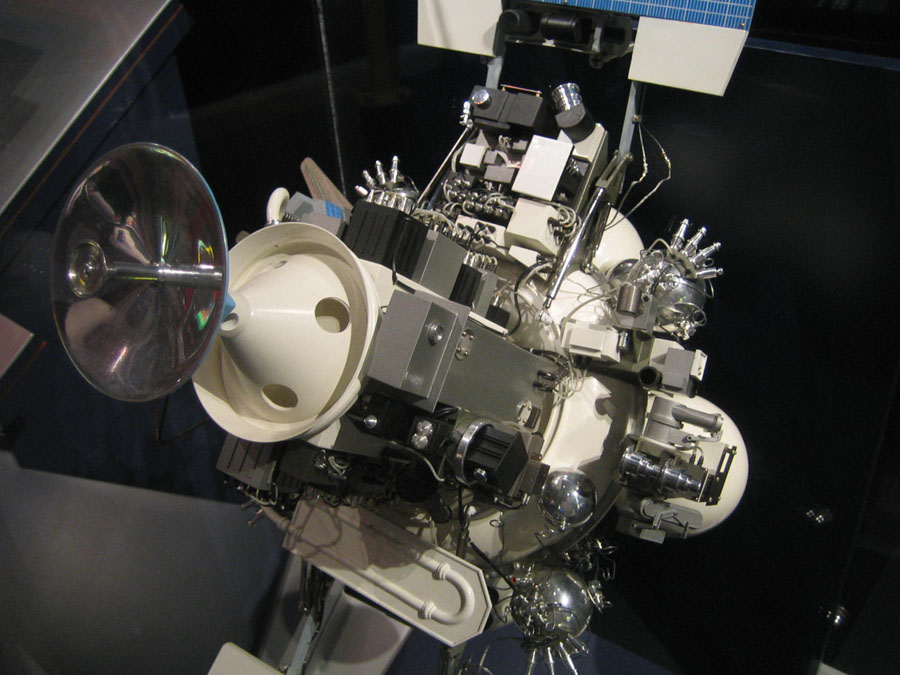
Recently seen here