
by Alex W. | Feb 2, 2018 | Cybersecurity, management and leadership, Organisations, Resilience
A speech given by Alex Webling to the opening of Z-CERT, the Hague, Netherlands, January 2018 Building better cyber security strategy in organisations The opening of Z-CERT is an important development in the protection of the Netherland’s health care system. I...

by Sasha | Mar 5, 2015 | management and leadership, Organisations, Resilience
Security Standards are vital to our society That’s why Alex Webling has accepted a nomination to join the Australian Standards Committee for Security Standards and to join the Australian Delegation to ISO TC292, Morioka, Japan in March 2015. We congratulate Alex...
by Alex W. | Dec 22, 2014 | Big data, Community and Society, Crime, Cybersecurity, Organisations
State of ICT Security – Attackers take over SCADA controlled steelworks furnace and caused massive damage The threat to online assets from attackers remains critical according to a report just released on the State of ICT security by the German Government. Cloud...
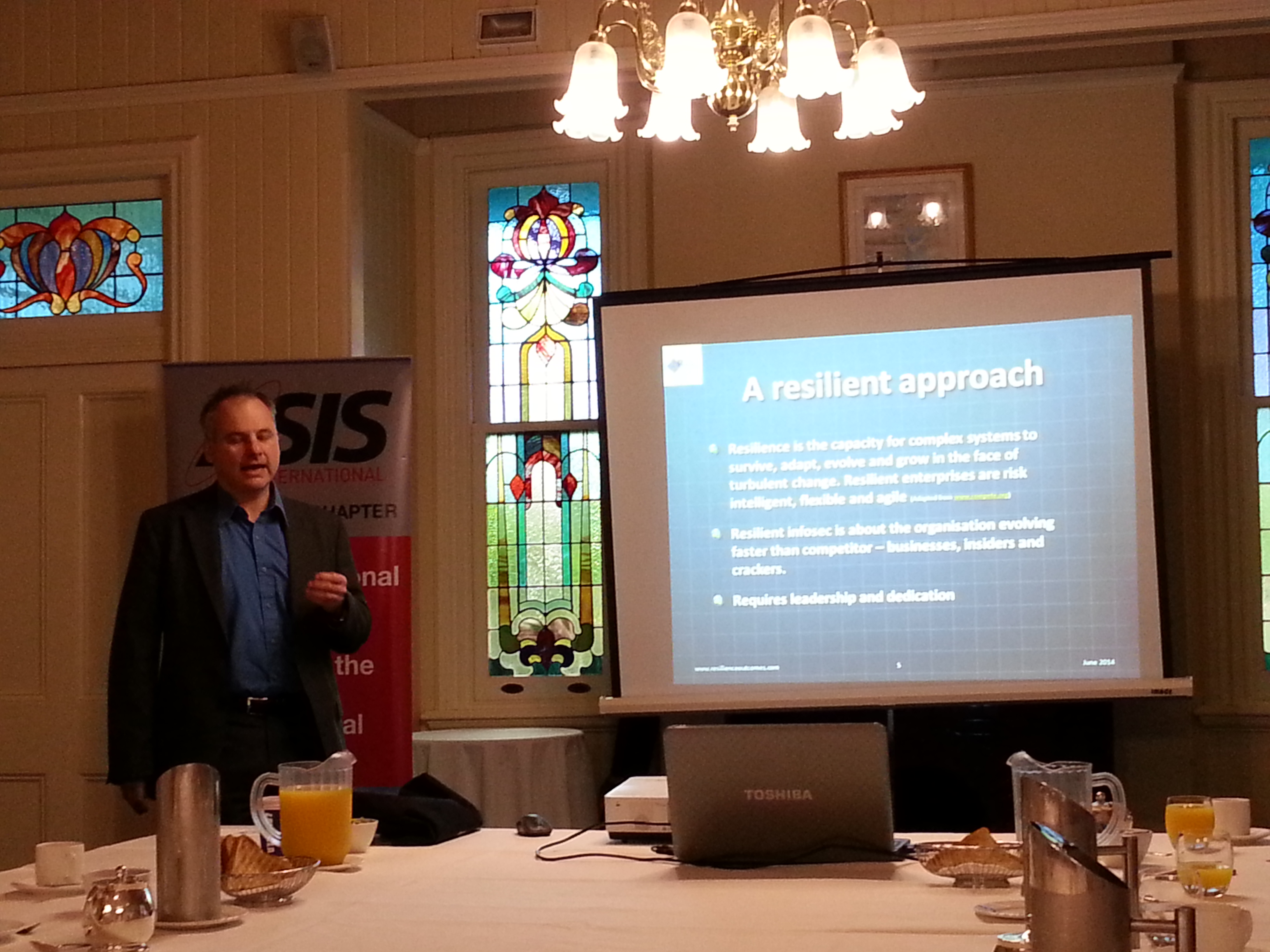
by Alex W. | Jun 12, 2014 | Cybersecurity, Organisations, Resilience
Information Security and Resilience presentation to ASIS QLD Chapter I gave a presentation to the ASIS QLD Chapter yesterday morning. Apart from a couple of minutes spruiking the Australasian Council of Security Professionals, I spent my time talking about the...
by Alex W. | Oct 30, 2013 | Cybersecurity, Government large and small
Over-classification in government continues to restrict information sharing according to a report by the US Department of Defense Inspector General. Balance in Information Security I’ve written previously about over-classification and why it needs to be actively...




Recently seen here